Many Exchange Server administrators know how to use features from Exchange Server 2003 which will not be available by default, if they do not use Exchange Server 2007 Edge Server Role as message hygiene server in the DMZ. This feature is only available within that role by default but can be enabled on each Exchange Server 2007 running Hub Transport Role. In this article we will have a look how to enable and configure this feature.
Activating AntiSpamAgent Feature
Adding this functionality to your Hub Transport servers is a pretty simple process. First, launch the Exchange Management Shell. In the Scripts folder that was created, you will find a PowerShell script to install the Anti-spam agents. After you run this command, you will need to restart your transport service and restart the Exchange Management Console. The script we need to run is called install-AntiSpamAgents.ps1.
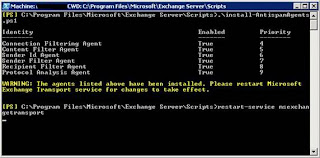
Figure 1: Activating AntiSpamAgent Feature
After restarting the Exchange Transport Service, we have a new tab in Exchange Management Console available which will look like this:
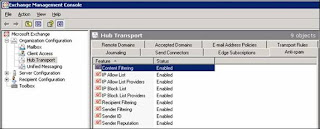
Figure 2: The Anti-Spam Tab of Exchange Management Console
Note:
We will now take a closer look into each feature of Anti-Spam:
Content Filtering
IP Allow List
IP Allow List Providers
IP Block List
IP Block List Providers
Recipient Filtering
Sender Filtering
Sender ID
Sender Reputation
Content Filtering
The Content Filter agents works with spam confidence level rating. This rating is a number from 0-9 for each message; a high SCL will mean that it is most likely spam. You can configure the agent according to the message ratings to:
Delete the message
Reject the message
Quarantine the message
You can also customize this filter using your own custom words and configure exceptions if you wish.
IP Allow List
With this feature you are able to configure which IP addresses are allowed to successfully connect to your Exchange Server. So, if you probably have a dedicated mail relay server in your DMZ, you can add its IP addresses so that your server will not accept connections from other servers anymore.
IP Allow List Providers
In general, you are unable to configure your own “IP Allow Lists” without making mistakes that will lead to problems receiving emails from your customers or any other business partners. Therefore, you should contact a public IP allow list provider which does the work for you. This would mean that you will have more quality in this service and a higher business value.
IP Block Lists
This feature gives you the possibility to configure IP addresses that are not allowed to connect to your server. Contrary to “IP Allow Lists”, this feature provides a black list and not a white one.
IP Block List Providers
“IP Block List Providers” have been known in the past as “Blacklist Providers” too. Their task is to publish lists from servers / IP addresses that are spamming.
Recipient Filtering
If you need to block emails to specific internal users or domains, this feature is the one you will need. You can configure this feature and then add the appropriate addresses or SMTP domains to your black list. Another interesting feature is that it allows you to set up the configuration so that only you will accept emails from recipients that are included in your global address lists.
Sender Filtering
If you need to block specific domains or external email addresses, you will have to use this feature. You can configure a black list of what sender addresses or domains you will accept or not.
Sender ID
The Sender ID agent relies on the RECEIVED Simple Mail Transfer Protocol (SMTP) header and a query to the sending system's domain name system (DNS) service to determine what action, if any, to take on an inbound message. This feature is relatively new and relies on the need of a specific DNS setting.
Sender ID is intended to combat the impersonation of sender and domain also called spoofing. A spoofed mail is an e-mail message that has a sending address that was modified to appear as if it originates from a sender other than the actual sender of the message. Spoofed mails typically contain a FROM in the header of a message that claims to originate from a dedicated organization.
The Sender ID evaluation process generates a Sender ID status for each message. The Sender ID status is used to evaluate the SCL rating for that message. This status can have one of the following settings:
Pass - IP address is included the permitted set
Neutral - Published Sender ID data is explicitly inconclusive.
Soft fail - IP address may be in the not permitted set.
Fail - IP address is in the not permitted set.
None - No published data in DNS.
TempError - transient error occurred, such as an unavailable DNS server
PermError - unrecoverable error occured, such as the record format error
The Sender ID status is added to email metadata and is then converted to a MAPI property. The Junk E-mail filter in Microsoft Office Outlook uses the MAPI property during the generation of the spam confidence level (SCL) value.
You can configure this feature to act as the following:
Stamp the status
Reject
Delete
Sender Reputation
Sender Reputation is a new Exchange Server 2007 anti-spam functionality that is intended to block messages based on many characteristics.
The calculation of the Sender Reputation Level is based on the following information:
HELO/EHLO analysis
Reverse DNS lookup
Analysis of SCL
Sender open proxy test
Sender reputation weighs each of these statistics and calculates an SRL for each sender. The SRL is a number between 0 and 9. You can then configure what to do with the message in one of the following ways:
Reject
Delete and archive
Accept and mark as blocked sender
Conclusion
As you have seen in this article, Exchange Server 2007 provides a lot of features to increase anti-spam functionality on each Exchange Server box. If you do not use a dedicated Exchange Edge Server, you can add this functionality to Exchange Server 2007 Hub Transport as described above. If you define a configuration for your specific server design, you will not have to add third party software to meet your basic business needs.
If you decide to have more than the described functions above, you should think of implementing Microsoft ForeFront Security for Exchange Servers.
2 comments:
Well I think that the above features are more than enough. They are very useful and will make the exchange servers more efficient and powerful. I have examined each and every feature that you have listed above. Thank you.
Do you recommend using it at my next server upgrade ?
Post a Comment